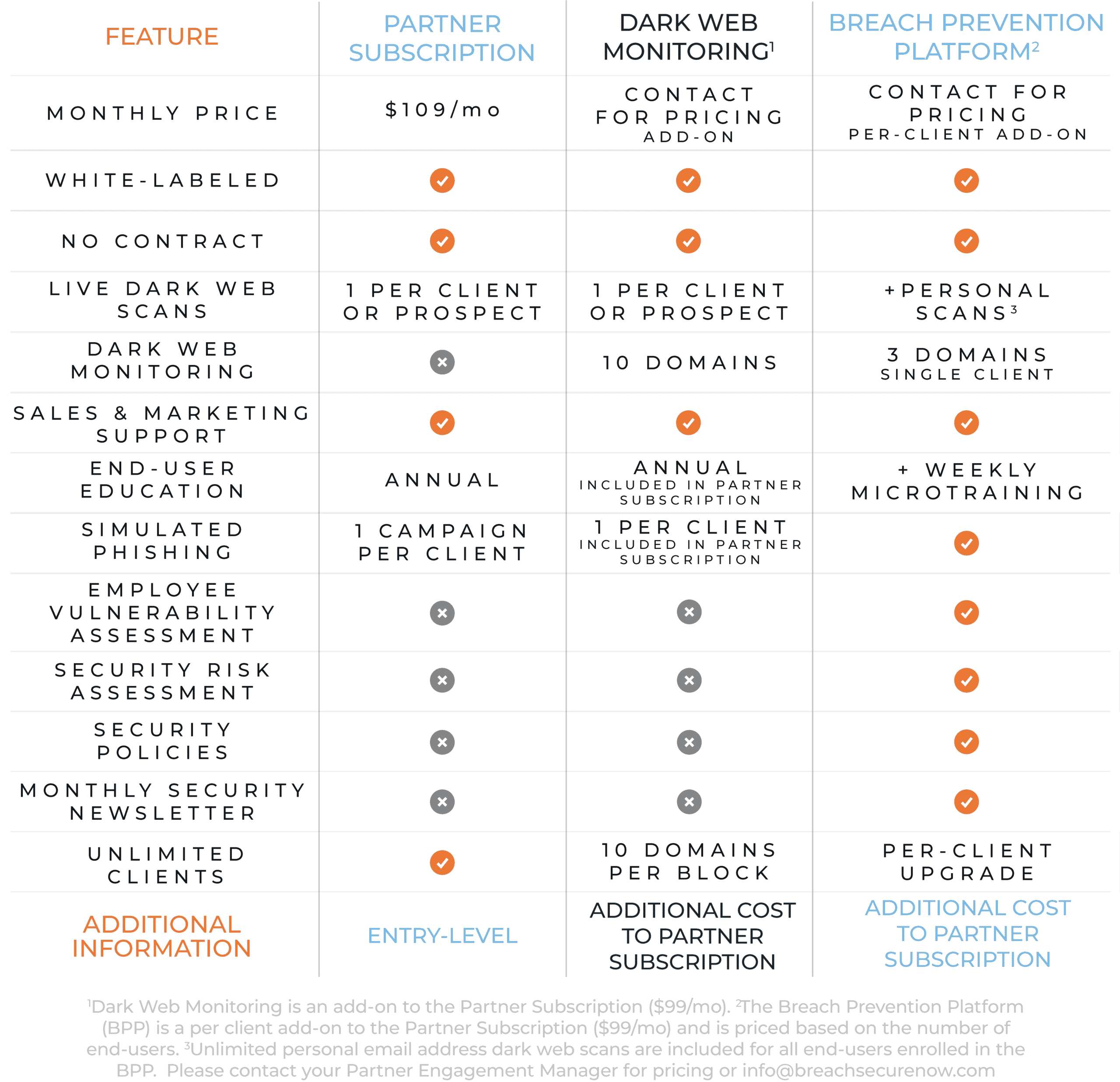
BREACH PREVENTION PLATFORM
Continuous Monitoring Equals
Consistent Protection
Why the Breach Prevention Platform (BPP)?
Now that you’ve performed a baseline assessment on your client, it’s time to provide remediation for the identified risks and position those risks to sell additional security services. This per-client upgrade provides continuous education and monitoring to keep security top-of-mind and help strengthen the weakest links, before it’s too late.
All it takes is one employee to cause a data breach
Cybercriminals are diligent in finding new, sophisticated methods to trick unsuspecting individuals into putting themselves at risk. Having a proactive approach is key in a robust security culture and our Employee Vulnerability Assessment is just the tool you need to help defend your clients' weakest links.
Real-time monitoring and management
Continuity is key for retention. Our Dark Web Monitoring, AutoPhish (unlimited, automated campaigns), annual training course, and weekly micro-training quizzes are all summarized into our real-time Employee Vulnerability Assessment dashboard, allowing convenient monitoring of your users.
EVA: The Heart of the BPP
EVA combines proven security metrics with quantitative analysis and friendly competition. Clients can watch as you strengthen their weakest employees into their strongest defenses.
How Does it Work?
EVA provides unparalleled insight into an organization's first layer of defense, their employees, by combining key security metrics with friendly competition.
Employee Secure Score (ESS)
Which employee is the weakest link?
The ESS uses a sophisticated algorithm of metrics to transform end-user education into an analytical engine. By assigning an ESS to each user, employees can see where they fall in their peer group and in what areas they can improve.
Company Overall ESS
How will you reduce their risk level?
By averaging all end-users' ESS, each organization is assigned a Company Overall ESS. Leveraging this score gives management insight into their overall security hygiene and highlights the need for technical safeguards.
End-User Education, Evolved
Training, Phishing, Dark Web, Security Policies, & an Interactive Portal - we cover it all.

Best MSP-Focused All-In-One End-User Education
A recent study revealed that 48% of hackers and incident responders spend 1-5 hours per week keeping up with security news, trends, and technologies, so why aren't we educating our clients' employees more than once a year?
The Nuix 2018 Black Report








